CVE-2026-1995
IDrive Cloud Backup Client for Windows contains a privilege escalation vulnerability
Description
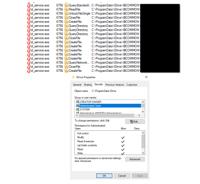
IDrive’s id_service.exe process runs with elevated privileges and regularly reads from several files under the C:\ProgramData\IDrive\ directory. The UTF16-LE encoded contents of these files are used as arguments for starting a process, but they can be edited by any standard user logged into the system. An attacker can overwrite or edit the files to specify a path to an arbitrary executable, which will then be executed by the id_service.exe process with SYSTEM privileges.
INFO
Published Date :
March 24, 2026, 7:16 p.m.
Last Modified :
March 25, 2026, 3:41 p.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2026-1995
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Limit write access to IDrive configuration files.
- Ensure only authorized users can modify these files.
- Consider running the service with least privilege.
- Apply vendor patches when available.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-1995.
| URL | Resource |
|---|---|
| https://kb.cert.org/vuls/id/330121 | |
| https://www.kb.cert.org/vuls/id/330121 |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-1995 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-1995
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-1995 vulnerability anywhere in the article.

-
Daily CyberSecurity
Microsoft Defender Zero-Day “BlueHammer” Hits KEV Catalog Following Researcher’s Protest
Image: Will Dormann CISA has officially added a fresh vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, citing evidence of active exploitation in the wild. The flaw, tracked as CVE-2 ... Read more

-
Daily CyberSecurity
Proof-of-Concept Released: Public Exploit Details for Windows Error Reporting LPE (CVE-2026-20817)
Researcher Clément Labro published a deep-dive analysis and a functional Proof-of-Concept (PoC) exploit for a critical security flaw in the Windows Error Reporting (WER) service. The vulnerability, tr ... Read more

-
CybersecurityNews
IDrive for Windows Vulnerability Let Attackers Escalate Privileges
A critical local privilege escalation vulnerability has been identified in the IDrive Cloud Backup Client for Windows. Tracked as CVE-2026-1995, this local privilege escalation vulnerability affects t ... Read more

-
Daily CyberSecurity
Public Flaws in Cisco IOx Allow Unauthenticated Log Injection and Admin XSS
Cisco has issued security advisories regarding two vulnerabilities in its Cisco IOx application hosting environment for Cisco IOS XE Software. The flaws, which include a stored cross-site scripting (X ... Read more
-
Daily CyberSecurity
The Backup Backdoor: How a Simple File Edit Grants Full SYSTEM Control in IDrive for Windows
A critical local privilege escalation vulnerability has been discovered in the IDrive Cloud Backup Client for Windows, potentially allowing low-privileged users to seize full control of an affected ma ... Read more
The following table lists the changes that have been made to the
CVE-2026-1995 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Mar. 25, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Mar. 24, 2026
Action Type Old Value New Value Added Reference https://www.kb.cert.org/vuls/id/330121 -
New CVE Received by [email protected]
Mar. 24, 2026
Action Type Old Value New Value Added Description IDrive’s id_service.exe process runs with elevated privileges and regularly reads from several files under the C:\ProgramData\IDrive\ directory. The UTF16-LE encoded contents of these files are used as arguments for starting a process, but they can be edited by any standard user logged into the system. An attacker can overwrite or edit the files to specify a path to an arbitrary executable, which will then be executed by the id_service.exe process with SYSTEM privileges. Added Reference https://kb.cert.org/vuls/id/330121